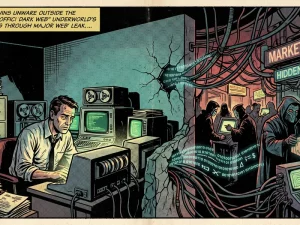
Not all hackers fit neatly into the categories of “good” or “bad.” As explored in“The Grey Hat Paradox: Guardians or Gatecrashers of the Digital World?”, some operate in the space between, neither fully malicious nor fully authorized. These are often referred to as grey hat hackers.
They may not intend to cause harm. In many cases, their goal is to expose vulnerabilities, raise awareness, or even help organizations improve their security. But despite these intentions, their actions introduce a different kind of risk, one that is often overlooked.
When Intent Doesn’t Define Impact
One of the biggest misconceptions around grey hat hacking is that good intentions reduce risk. In reality, intent does not determine the impact. Accessing a system without permission, even to identify a vulnerability, is still unauthorized. It can disrupt operations, expose sensitive data, or trigger security responses that escalate the situation unnecessarily. From an organizational perspective, the result matters more than the motivation behind it.
The Problem with Uninvited Testing
Grey hat hackers often engage in what can be described as unauthorized security testing. They scan systems, probe weaknesses, and sometimes even exploit vulnerabilities, all without formal approval. This creates uncertainty.
Organizations may not know who is accessing their systems, what is being tested, or how far the activity will go. What might be intended as a harmless test can quickly resemble a real attack, making it difficult to respond appropriately. In some cases, it can even interfere with ongoing operations or security processes.
A Legal and Operational Risk
Beyond technical concerns, grey hat hacking introduces legal complexity. Unauthorized access is still a violation in many jurisdictions, regardless of intent. This creates risk on both sides. For the hacker, actions can lead to legal consequences or misidentification as a malicious actor. For organizations, responding to such incidents can involve investigations, compliance considerations, and potential reputational impact. What begins as an attempt to “help” can evolve into a situation that requires serious response.
The Visibility Challenge
Another challenge is visibility. When authorized security testing is conducted, it is planned, monitored, and documented. Teams know what is being tested and can respond accordingly. With grey hat activity, none of this structure exists.
Security teams may detect unusual behavior without context, leading to confusion or delayed response. This lack of clarity makes it harder to distinguish between genuine threats and unauthorized testing.
Why Structure Matters in Security
Modern cybersecurity is built on coordination and control. Testing is essential, but it needs to happen within defined boundaries. Authorized approaches such as penetration testing and vulnerability disclosure programs provide a structured way to identify and address weaknesses. They ensure that testing is conducted safely, legally, and with full visibility. This allows organizations to benefit from external expertise without introducing unnecessary risk.
Moving Toward Responsible Security Practices
Grey hat hacking highlights the gap between intention and execution. It shows that even well-meaning actions can create real consequences when they operate outside defined boundaries.
As cyber threats continue to evolve, organizations need reliable and structured ways to test and strengthen their defenses. At the same time, individuals with the skills to identify vulnerabilities need clear and legitimate paths to contribute. Bridging this gap is key to building a more secure digital environment.
Through Terrabyte, organizations can explore modern cybersecurity strategies that emphasize controlled testing, clear processes, and responsible practices, ensuring that efforts to improve security do not unintentionally create new risks.