In the previous article, “Potential Insider Threat Indicators Every Organization Should Know,” we explored common behavioral and technical warning signs that may signal internal security concerns. While identifying these indicators is an important first step, recognizing warning signs alone does not fully capture the broader issue organizations face today.
Insider threat risk extends beyond isolated suspicious behaviors. It represents the potential business, operational, financial, and reputational impact that can arise when trusted individuals misuse access intentionally or unintentionally. To manage insider risk effectively, organizations must move from observing indicators to understanding exposure at a structural level.
Why Indicators Alone Do Not Define Risk
Warning signs such as unusual login times, bulk file downloads, or privilege escalation attempts may signal suspicious activity. However, isolated indicators do not automatically equate to high risk. Risk emerges when multiple contextual factors intersect, such as:
- The sensitivity of the accessed data
- The user’s role and privilege level
- Behavioral deviations from established patterns
- Timing related to employment status changes
- Access outside normal operational requirements
Without contextual analysis, organizations may either underestimate genuine threats or overreact harmless anomalies. A true insider threat risk assessment requires correlating behavior with business impact.
The Business Impact of Insider Threat Risk
Insider-related incidents can lead to consequences that extend far beyond data leakage. Depending on the industry and type of compromised information, impacts may include:
- Regulatory penalties and compliance violations
- Intellectual property loss
- Financial fraud
- Operational disruption
- Reputational damage and loss of customer trust
Because insiders often understand internal systems and processes, their actions may bypass conventional security controls, increasing the potential severity of an incident.
Insider Threat Risk in Modern Digital Environments
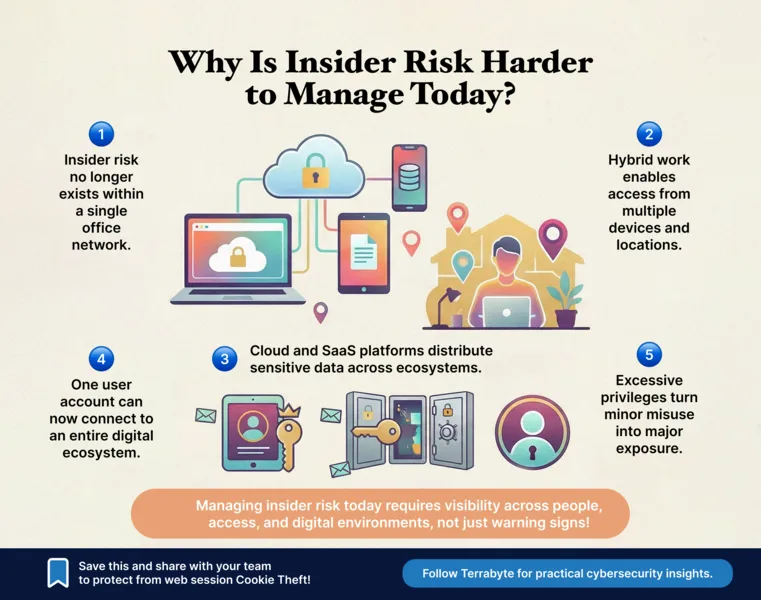
Hybrid work models, cloud adoption, and distributed collaboration have expanded the insider risk landscape. Employees now access critical systems from multiple devices and locations. Sensitive data flows across endpoints, SaaS platforms, and shared environments.
This distributed access model increases complexity and reduces traditional visibility. As a result, insider threat risk is no longer confined to on-premises environments; it extends across digital ecosystems where monitoring and contextual awareness must evolve accordingly. Organizations must therefore view insider risk as an ongoing exposure tied to access governance, behavioral transparency, and operational oversight.
Advancing Insider Risk Awareness with Terrabyte
Recognizing potential indicators is an essential starting point. However, sustainable security programs require deeper evaluation of insider threat risk across people, processes, and technology. Understanding insider threat risk is a critical step toward building a mature security posture.
At Terrabyte, we help organizations strengthen their visibility into internal risk exposure through structured assessment, monitoring alignment, and enterprise-focused security strategies. By elevating insider risk discussions from isolated indicators to comprehensive risk evaluation, Terrabyte supports enterprises in improving resilience, governance, and long-term operational stability.