In the previous article, “Real-Life Data Breach Cases: What Happens When SSL Fails?”, we explored how misconfigured or failed SSL encryption can expose sensitive data to attackers. These incidents showed that even widely trusted security technologies can become points of vulnerability when not properly implemented or maintained.
However, understanding what went wrong is only part of the solution. The more important question is: how can organizations protect their data and prevent similar incidents from happening?
Why SSL Alone Is Not Enough
SSL (Secure Sockets Layer) and its successor TLS are essential for encrypting data in transit. They help protect information such as login credentials, financial transactions, and personal data from being intercepted.
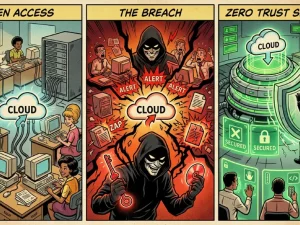
But SSL is only one layer of security. When it is misconfigured, expired, or improperly managed, it can create a false sense of protection. Attackers can exploit these weaknesses to intercept or manipulate data. This is why organizations must go beyond relying solely on encryption and adopt a broader data protection strategy.
Step 1: Ensure Proper SSL/TLS Configuration
The first step is to make sure that SSL/TLS is correctly implemented and continuously maintained. This includes using strong encryption protocols, valid certificates, and secure configurations. Organizations should regularly review their SSL settings to ensure there are no vulnerabilities, such as outdated protocols or weak cipher suites. Certificate management is also critical; expired or improperly installed certificates can expose systems to unnecessary risk. Proper configuration ensures that encryption works as intended.
Step 2: Monitor and Detect Security Gaps
Even with strong encryption in place, organizations need visibility into how data is transmitted and accessed. Monitoring tools can help detect unusual traffic patterns, misconfigurations, or potential interception attempts. Continuous monitoring allows security teams to identify issues early before they escalate into full-scale breaches. It also provides valuable insights into how data flows across systems. Without visibility, vulnerabilities may remain undetected.
Step 3: Protect Data Beyond Transmission
One of the key lessons from SSL-related breaches is that protecting data in transit is not enough. Organizations must also secure data at rest and during usage. This means implementing controls that prevent unauthorized access, copying, or sharing sensitive information even after it has been decrypted and displayed to users. By extending protection beyond transmission, organizations reduce the risk of data exposure at multiple stages.
Step 4: Strengthen Access Control
Limiting access to sensitive data is essential for reducing risk. Organizations should ensure that only authorized users can access critical systems and information. This includes implementing multi-factor authentication, role-based access control, and regular reviews of user permissions. Strong access control reduces the impact of potential vulnerabilities, including those related to SSL failures.
Step 5: Conduct Regular Security Assessments
Regular security assessments help organizations identify weaknesses before attackers do. This includes vulnerability scanning, penetration testing, and configuration reviews. By proactively testing systems, organizations can detect SSL misconfigurations and other security gaps early. This reduces the likelihood of real-world exploitation. Security is not a one-time setup; it requires continuous evaluation.
Step 6: Educate Teams and Improve Awareness
Human errors can contribute to security incidents, including SSL mismanagement. Teams responsible for maintaining systems must understand the importance of proper configuration and ongoing monitoring. Providing training and clear guidelines helps reduce the risk of mistakes that could lead to vulnerabilities.
From Lessons to Action
Real-life SSL failure cases highlight a critical truth: no single security control is enough to protect data on its own. Organizations must adopt a layered approach that combines encryption, monitoring, access control, and continuous improvement. By learning from past incidents and implementing proactive measures, businesses can significantly reduce the risk of data exposure.
SSL plays a vital role in protecting data, but it must be part of a broader security strategy. Misconfigurations and gaps in visibility can turn a trusted technology into a vulnerability. By focusing on proper configuration, continuous monitoring, and comprehensive data protection, organizations can better safeguard their sensitive information.
Terrabyte helps organizations strengthen their cybersecurity strategies by implementing reliable data protection practices and ensuring that critical systems are secure in today’s evolving threat landscape.