In the previous article, “Potential Insider Threat Indicators Every Organization Should Know,” we discussed common warning signs that may signal suspicious internal behavior. While recognizing these indicators is important, awareness alone does not stop incidents from occurring. Organizations must move beyond detection and develop structured strategies to prevent insider threats before damage takes place.
Preventing insider threats requires a proactive, layered approach that addresses people, processes, access control, and continuous monitoring. As digital environments become more distributed, insider threat prevention must evolve from reactive alert handling into an integrated security framework.
Why Prevention Requires More Than Monitoring
Many organizations rely heavily on alerts and logs to identify unusual activities. However, prevention is not the same as detection. By the time suspicious activity is flagged, sensitive data may already have been exposed.
Effective insider threat prevention focuses on minimizing risk exposure early, before misuse, negligence, or compromised credentials lead to significant impact. This requires governance, access discipline, and behavioral oversight aligned with business operations.
Key Strategies to Prevent Insider Threats
A strong insider threat prevention program is built on structured controls and clear policies. It typically includes:
- Access Governance and Least Privilege
Limiting user access strictly to what is necessary reduces the opportunity for misuse. Regular access reviews and role-based permissions are critical. - Data Classification and Visibility
Organizations must understand where sensitive data resides and who interacts with it. Without data visibility, prevention efforts lack direction. - User Activity Monitoring with Context
Monitoring should establish behavioral baselines and detect deviations early. Contextual awareness helps identify emerging risks before they escalate. - Security Awareness and Training
Many insider incidents result from negligence rather than malicious intent. Continuous education helps reduce accidental exposure. - Clear Incident Escalation Procedures
Prevention includes readiness. Clear workflows ensure rapid action when risk signals appear.
Together, these elements reduce both intentional and unintentional insider-driven incidents.
Aligning Prevention with Modern Work Environments
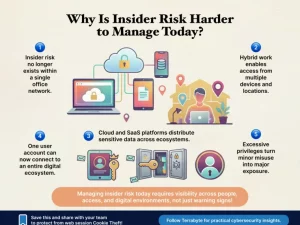
Hybrid work, remote access, and cloud adoption have expanded access boundaries. Employees now interact with corporate data across endpoints, SaaS applications, and external networks.
To prevent insider threats effectively, security controls must extend across distributed environments. Access to governance, behavioral monitoring, and policy enforcement should operate consistently, regardless of location or device. Prevention is strongest when visibility and accountability are embedded into daily workflows rather than applied only during investigations.
When employees understand the importance of data protection and the consequences of misuse, prevention becomes part of operational discipline rather than a reactive security measure.
Strengthening Insider Threat Prevention with Terrabyte
Technology alone cannot eliminate insider threats. Organizational culture plays a critical role. Clear policies, leadership commitment to data protection, and transparent communication create an environment where security becomes a shared responsibility.
At Terrabyte, we help organizations design and implement structured insider threat prevention strategies aligned with enterprise governance and operational needs. By integrating access control, visibility frameworks, and contextual monitoring into a cohesive approach, Terrabyte supports businesses in reducing insider-driven risks while maintaining productivity and compliance readiness.