As organizations continue their digital transformation journeys, the traditional concept of endpoint security is rapidly evolving. Employees now access corporate systems through laptops, mobile devices, and remote workstations connected from various locations. At the same time, applications and workloads increasingly operate in cloud environments rather than on-premises infrastructure.
This shift has created new challenges for security teams. Traditional endpoint protection tools designed for fixed office networks are often insufficient in distributed environments. As a result, organizations are turning to endpoint security cloud solutions to ensure consistent protection across devices, regardless of where users are working.
What Is Endpoint Security Cloud?
Endpoint security cloud refers to a cloud-based approach to protecting endpoints such as laptops, desktops, servers, and mobile devices. Instead of relying solely on locally installed security tools, protection and monitoring capabilities are delivered through centralized cloud platforms.
This architecture enables security teams to manage endpoint protection across geographically distributed environments while maintaining real-time visibility into device activity and potential threats. Cloud-driven endpoint security platforms typically provide capabilities such as malware detection, behavioral monitoring, threat intelligence integration, and centralized policy management.
Why Traditional Endpoint Security Is No Longer Enough
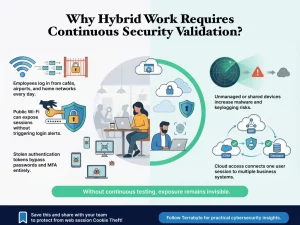
In the past, endpoint protection was designed primarily for office-based networks where devices operated within clearly defined perimeters. However, modern work environments are far more dynamic. Several factors have increased the complexity of endpoint security:
- Hybrid and remote work environments
- Increased use of cloud-based applications
- Expansion of unmanaged or personal devices
- Sophisticated malware and ransomware campaigns
- Rapid growth of distributed corporate networks
Without cloud-based visibility and control, security teams may struggle to maintain consistent protection across this expanded digital landscape.
Key Benefits of Cloud-Based Endpoint Security
Adopting an endpoint security cloud approach enables organizations to strengthen their protection while improving operational efficiency. By leveraging cloud infrastructure, security teams can implement scalable and flexible defenses that adapt to evolving threats. Key advantages include:
- Centralized Security Management
Cloud platforms allow security teams to monitor and manage endpoints from a single dashboard.
- Real-Time Threat Intelligence
Cloud-based systems can rapidly integrate global threat intelligence updates to improve detection accuracy.
- Scalable Protection Across Devices
As organizations grow, new endpoints can be integrated into the security framework without complex infrastructure changes.
- Improved Visibility into Endpoint Activity
Continuous monitoring enables early detection of suspicious behavior and potential compromise.
These capabilities help organizations maintain stronger defensive posture across distributed work environments.
Endpoint Security Cloud in Modern Cybersecurity Strategy
Endpoint devices are often the first entry point for attackers attempting to infiltrate corporate networks. Phishing attacks, malicious downloads, and credential compromise frequently begin at the endpoint level.
Integrating endpoint security cloud solutions into broader cybersecurity strategies helps organizations strengthen their defensive layers. When combined with network monitoring, identity management, and security analytics, endpoint protection becomes part of a comprehensive security ecosystem. This integrated approach is essential for organizations managing complex infrastructures across cloud, hybrid, and remote environments.
Strengthening Endpoint Security with Terrabyte
At Terrabyte, we help organizations enhance their cybersecurity posture by implementing modern endpoint security strategies aligned with cloud-driven infrastructures. Through structured security frameworks and integrated protection approaches, Terrabyte supports enterprises in securing distributed endpoints while maintaining visibility, control, and resilience against evolving cyber threats.