In the previous article, “Understanding Web Session Cookie Theft: How to Protect Your Online Sessions,” we explored how attackers exploit session cookies to hijack authenticated user sessions. The discussion focused on how stolen cookies can bypass login mechanisms and allow unauthorized access without needing credentials. While those risks remain relevant, the conversation must now evolve.
As organizations migrate applications to cloud and hybrid environments, session security becomes more complex. Web session cookie theft is no longer just a browser-level concern; it is a cloud application security issue that affects distributed architectures, APIs, and globally accessible services.
Why Session Cookie Theft Is More Dangerous in the Cloud
In traditional environments, applications were often hosted within tightly controlled infrastructure. Today, cloud-hosted applications are accessible from anywhere, scale dynamically, and interact with multiple backend services. This expanded exposure increases the impact of compromised session cookies.
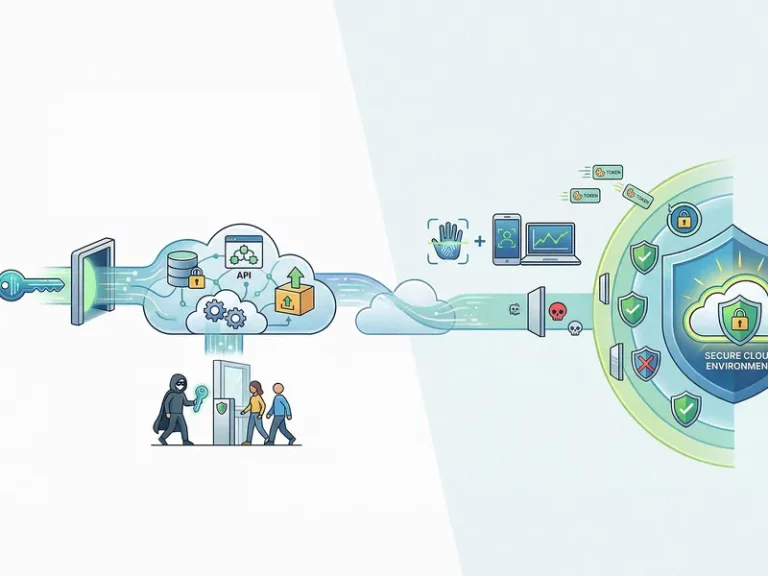
When attackers obtain valid session tokens through phishing, malware, cross-site scripting (XSS), or unsecured networks, they can impersonate legitimate users without triggering standard authentication alerts. In cloud environments, where applications connect to databases, storage services, and third-party APIs, a hijacked session can provide broad access across integrated systems. The distributed nature of cloud architecture amplifies both reach and speed of exploitation.
The Role of Identity and Token Management
Cloud applications rely heavily on tokens, cookies, and federated identity systems to maintain seamless user experiences. However, improper session expiration policies, weak cookie attributes, or insufficient encryption create opportunities for exploitation.
Secure cloud session management requires:
- Enforcing secure and HTTP-only cookie flags
- Implementing short-lived session tokens
- Binding sessions to device or behavioral attributes
- Applying continuous authentication checks
- These controls help reduce the likelihood that stolen session cookies can be reused successfully.
Application-Layer Threats in Distributed Environments
Web session cookie theft often occurs in conjunction with other application-layer attacks. Cross-site scripting vulnerabilities can expose cookies, while bot-driven automation can exploit hijacked sessions at scale. In cloud environments, these threats are harder to detect because traffic originates from legitimate authenticated sessions.
Traditional perimeter defenses are insufficient in these scenarios. Cloud application security must incorporate behavioral analysis, anomaly detection, and real-time inspection to identify suspicious activity, even when requests appear valid. Protecting session integrity requires visibility beyond login events.
Leveraging Edge and Cloud Security Controls
To mitigate session hijacking risks effectively, organizations must integrate protection mechanisms closer to the user interaction layer. Edge-based inspection, web application firewalls (WAF), and bot management solutions help detect abnormal session behavior before it reaches origin infrastructure.
By analyzing traffic patterns, enforcing adaptive policies, and filtering malicious requests early, organizations can reduce attacker dwell time and prevent large-scale exploitation of stolen session cookies. This approach aligns session security with broader cloud resilience strategies.
Strengthening Cloud Session Security with Terrabyte
At Terrabyte, we help organizations enhance cloud application security by integrating identity controls, application-layer protection, and distributed monitoring into a cohesive strategy. By aligning session management with modern cloud and edge architectures, Terrabyte supports enterprises in protecting user sessions, reducing hijacking risks, and maintaining trust across globally accessible digital services.